I still remember the day I saw someone install an IoT device in a smart building — right next to the fire escape — using the default login credentials of “admin/admin.” I nearly dropped my coffee.
“You’re trusting a multi-million-ringgit infrastructure to a sensor with no password policy?”
And that’s the thing about IoT.
We’re racing to connect everything — from lightbulbs to locomotives — but often forgetting one simple truth:
The more we connect, the more we expose.
And as someone who has worked in IoT, telco, and smart city development for over three decades, I’ve seen this cycle repeat itself — faster with every technological leap.
So when I was invited to speak at The Star Cybersecurity Summit in July 2025, I knew exactly what I wanted to share:
Connecting More Devices, Creating More Danger
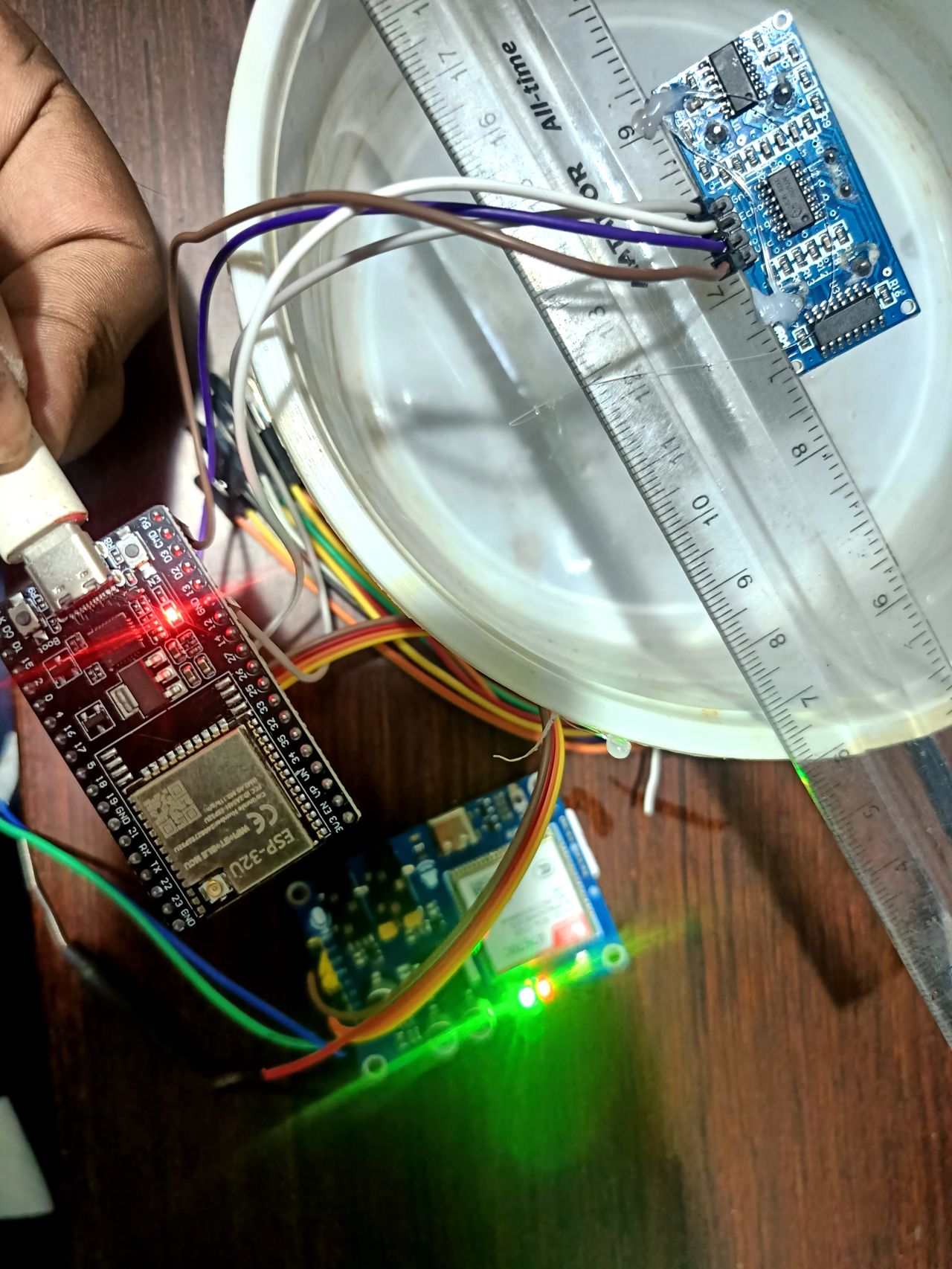
In today’s smart systems — whether they are smart cities, factories, farms, or homes — edge devices play a starring role.
These devices are like frontline scouts. They gather real-time data, process information locally, and sometimes even make autonomous decisions. But just like scouts, they’re vulnerable.
Here are the most significant cybersecurity risks I’ve seen firsthand when we connect more edge devices:
1. Weak Device Security
Most edge devices are small, cheap, and mass-produced. Security is often an afterthought.
Some still use:
- Outdated firmware
- Default credentials
- Open ports
- Unencrypted communications
And yet — we trust them to monitor our elderly, run our factories, and manage our city traffic.
It’s like giving the keys to your home to someone who doesn’t lock their own doors.
2. No Real-time Monitoring
Once deployed, many devices are left unattended — no logs, no updates, no alerts.
I call this the “fire and forget” problem.
Until something breaks… or gets hacked.
3. Firmware Tampering and Device Hijacking
If a hacker gets into your sensor, they can:
- Inject fake data
- Disrupt your entire network
- Turn your devices into zombie bots for a DDoS attack
Remember the Mirai botnet? It weaponised millions of unsecured IoT cameras. The same could happen with smart meters, parking sensors, or industrial controllers.
4. Supply Chain Vulnerabilities
When your edge devices come from dozens of unknown vendors — often with no transparency — you risk installing trojans at scale.
Imagine building your smart hospital system with sensors embedded with backdoors. Scary? It’s already happened.
5. Lack of Standardisation
Different vendors. Different protocols. No unified security framework.
It’s a hacker’s playground.
How AI Can Step In (and Save the Day)
I’ve seen how Artificial Intelligence is evolving from a buzzword into a battlefield necessity.
AI isn’t just about chatbots and analytics anymore — it’s now the guardian of the edge.
Here’s how:
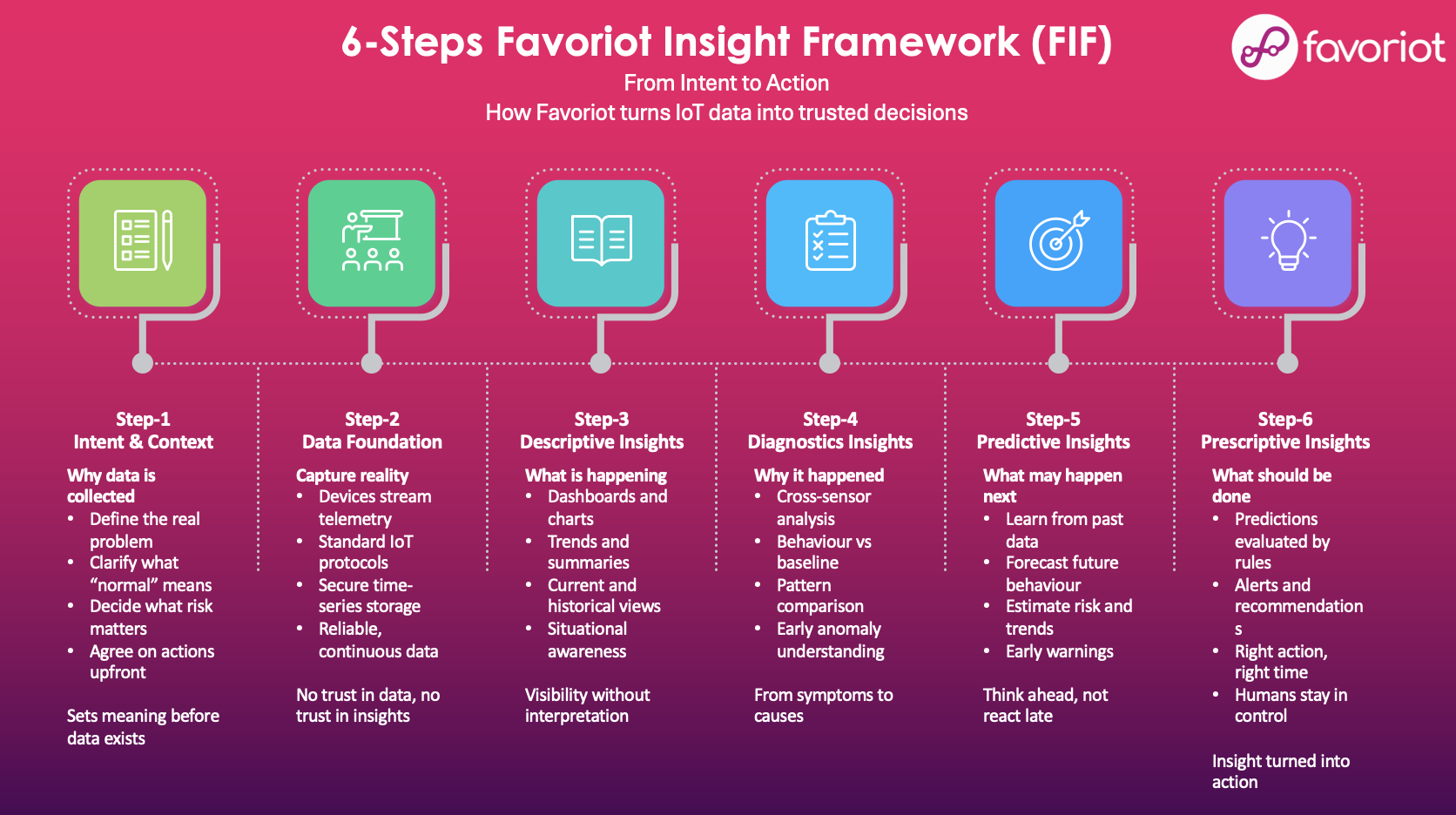
1. AI-Powered Anomaly Detection
AI models can learn what “normal” device behaviour looks like — and flag the weird stuff.
- A sensor that suddenly starts transmitting too frequently?
- A temperature spike that doesn’t match historical patterns?
- A device trying to connect to an unknown server?
AI catches what human eyes miss — and faster.
2. Behavioural Analytics
Instead of just checking for known threats (signatures), AI can profile user and device behavior over time.
It’s like having a cybersecurity guard dog that barks when something just feels off.
3. Faster Incident Response
With the help of AI, systems can:
- Isolate rogue devices
- Roll back firmware
- Trigger alerts
- Even patch known exploits — autonomously
All before your IT team finishes lunch.
4. Threat Intelligence at Scale
AI can analyse petabytes of threat data:
- Dark web chatter
- Zero-day exploit patterns
- Malware evolution
It becomes your real-time analyst — working 24/7, never sleeping, never distracted.
Looking Ahead: Beyond AI
During the summit, I was asked:
“Dr. Mazlan, beyond AI, which technology do you think will have the greatest impact on cybersecurity by 2030?”
I paused.
Then I said:
“It’s not one technology — it’s the convergence of many.”
Here’s what I believe will shape cybersecurity’s future:
1. Edge AI + Federated Learning
Imagine AI models trained locally on your edge devices — without sending raw data to the cloud. Privacy preserved. Speed increased.
It’s already happening in healthcare and smart manufacturing.
2. Post-Quantum Cryptography
Quantum computers are coming. And they will break today’s encryption.
We need to prepare now — using encryption that even quantum machines can’t crack. Or we’ll be decrypting our doom.
3. Blockchain for Device Identity and Audit
Every IoT device has a digital identity. Blockchain can help ensure it’s:
- Verifiable
- Immutable
- Transparent
Think of it as a passport for every device.
4. Digital Twins for Cyber Simulation
Want to test how your system would respond to a cyberattack — without risking your tangible assets?
Enter the digital twin. Simulate—stress test. Harden.
What Organisations Must Do Today
In the lightning round, the moderator asked us to give one practical step organisations should take right now.
Mine was simple:
“Adopt a Zero Trust mindset — and let AI be your sentry.”
Don’t assume any device, user, or system is trustworthy by default. Verify everything. Monitor always.
And pair that with AI systems that never blink.
Final Thoughts
I often tell young engineers this:
“Building smart cities is easy. Building safe ones? That’s the real challenge.”
We’re entering an era where cybersecurity is public safety.
Where edge devices are both our helpers and our weaknesses.
Where AI becomes not just a tool, but a necessity.
So the next time you deploy a new sensor or a smart controller, ask yourself:
“Have I made it smart enough to help… but safe enough to trust?”
Because in the race to connect everything — we must not disconnect from our responsibility to protect.
Let’s build the IoT world. But let’s build it securely.
And maybe, just maybe, we’ll sleep better knowing AI is on patrol — even when we’re not.
Dr. Mazlan Abbas is the CEO of FAVORIOT, Vice-Chairman of MyIoTA, and a lifelong advocate for secure, ethical, and inclusive IoT ecosystems.




Leave a Reply